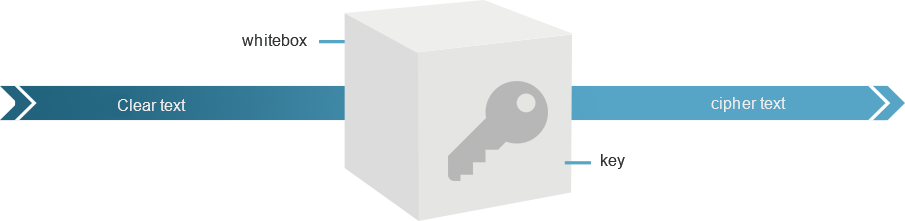
Key Whitebox
iJiami Key Whitebox, a cryptographic function-based computing technology, provides integrated and powerful protection for the encryption algorithm and its key, which not only enhances the encryption strength but also protects its own key in a relatively safer way. Meanwhile, iJiami Key Whitebox SDK supports one-time pad to provide high level security for the program's internal data, local data/ files and communication data.
Contact Sales